Phishing attacks use device codes to breach 340 Microsoft 365 organisations
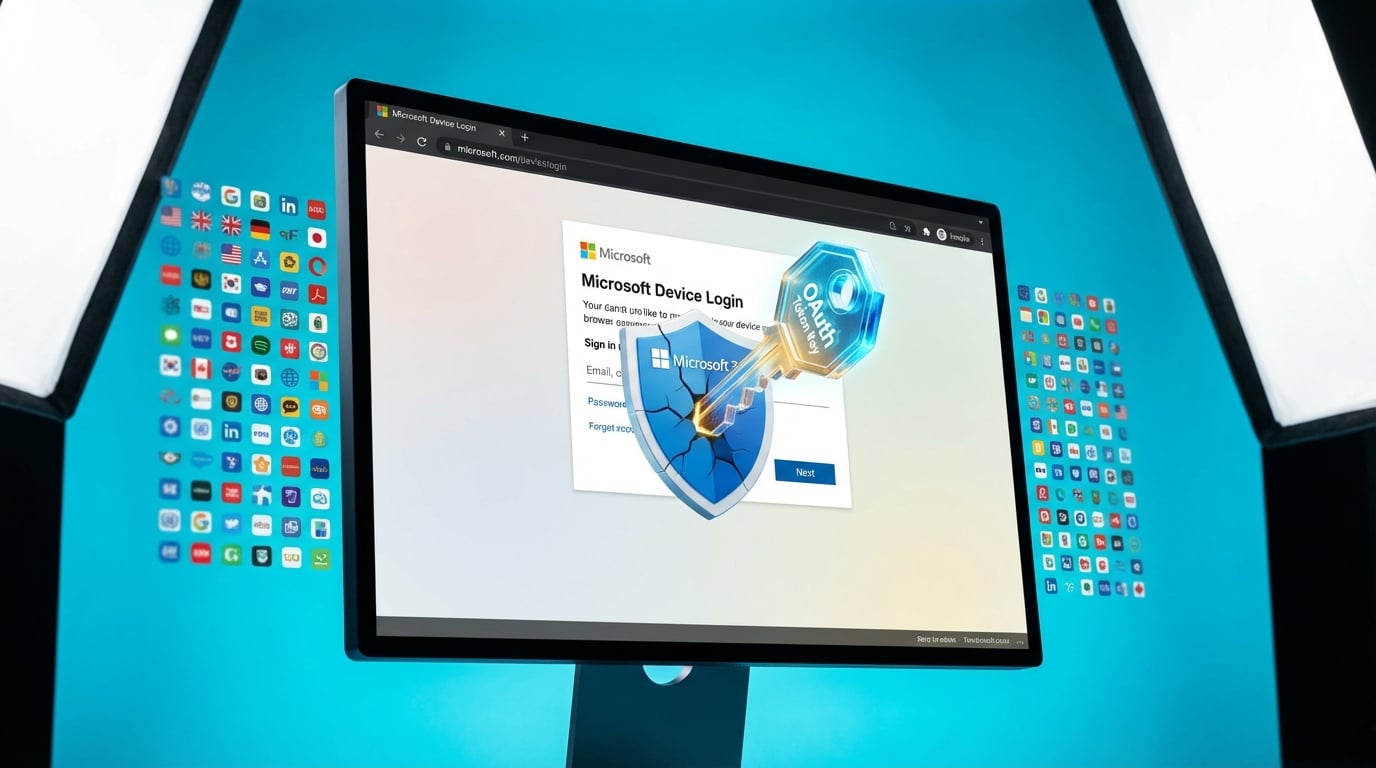
Cybersecurity researchers have uncovered a phishing campaign targeting Microsoft 365 accounts through the OAuth device authorisation flow. Attackers send emails with malicious links that route through Cloudflare Workers and Railway services to fake login pages at microsoft.com/devicelogin. Victims enter a device code and credentials, handing over tokens for ongoing access. The attacks have hit over 340 organisations in the United States, Canada, Australia, New Zealand and Germany since February 19, 2026. Three Railway IP addresses handle 84 percent of the traffic. Tokens allow persistent entry even after password resets. Defences include checking Entra ID sign-in logs for suspicious device code events and revoking refresh tokens.
Before this campaign, phishing attacks were often blocked by email filters or stopped with a simple password reset. Compromised accounts could be locked down quickly without deeper investigation. These attacks bypass spam detection by mimicking legitimate security flows and create backdoors through stolen tokens. Organisations now face repeated breaches unless they monitor sign-in logs and actively revoke tokens, turning a one-off incident into a routine security task.
Analysis
Log into the Microsoft Entra admin center, go to sign-in logs, and filter for device code authorisation events over the past month. Look for logins from the three main Railway IPs and revoke any suspicious refresh tokens.
Citation
This executive briefing was curated and analyzed by Collab365. To reference this analysis, please attribute: "This briefing is available on Collab365 Spaces (spaces.collab365.com)".