Hackers spoof IT support calls in Microsoft Teams to spread password-stealing malware
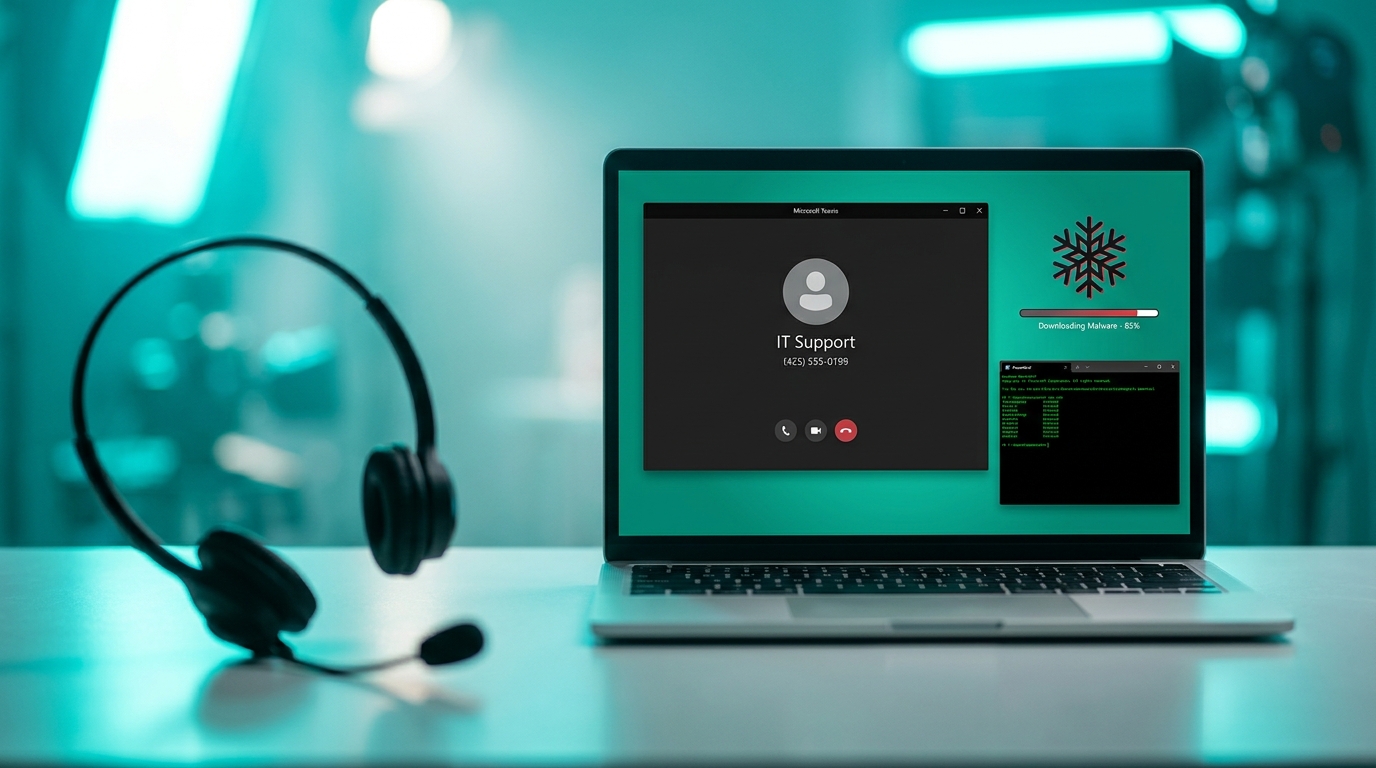
Threat actors are flooding email inboxes with spam messages that warn of IT issues. They follow up with incoming Microsoft Teams calls from external accounts, posing as support staff to build trust. Victims are tricked into running malicious PowerShell code that deploys Snow malware. This tool steals login credentials and opens a backdoor for remote control of infected machines. The attack targets organisations with Teams external access or guest accounts enabled, relying on user mistakes rather than technical flaws.
Teams guest access once seemed a harmless way to loop in partners or contractors, with admins relying on user caution to block fakes. Sprawled environments made spot checks rare, as hundreds of teams hid inactive guests from years ago. Now external calls emerge as a prime social engineering vector, turning every enabled guest policy into a spam-to-infection highway. Abandoned teams amplify the danger, making cleanup non-optional before any Copilot rollout.
Analysis
Your Teams sprawl just became a live threat vector – those lingering guests from ex-contractors are sitting ducks for this exact scam. Forget blanket disabling that sparks user revolts; export the guest access report from the Teams admin center today and revoke every account inactive for over 90 days.
Citation
This executive briefing was curated and analyzed by Collab365. To reference this analysis, please attribute: "This briefing is available on Collab365 Spaces (spaces.collab365.com)".